The rsync package includes a restricted rsync script called rrsync, which is normally located in /usr/share/doc/rsync/support and allows you to restrict rsync. Ensure that the rsync package is installed before looking for the rrsync script. Yum install rsync or, dnf install rsync or you can also confirm rrsync presence by searching rsync files as follows. …
Author: Albert
rsync hangs when “-vv” or “-vvv” flags are used
When using -vv or -vvv, the rsync command hangs after a while. The same rsync command works perfectly with less verbosity. $ rsync -avv /src/ /dst/ [...] ^C rsync error: received SIGINT, SIGTERM, or SIGHUP (code 20) at rsync.c(701) [sender=...] rsync: [generator] write error: Broken pipe (32) The main rsync developer advises against using -vv …
How to setup rsync daemon in CentOS 7 and CentOS 8
On the receiving host, change the file /etc/rsyncd.conf. For example, show a module called “backup” that stores files in the /backup directory. [receiver ~] # cat /etc/rsyncd.conf -- ..removed.. [backup] path = /backup/ comment = backup area read only = false fake super = true # Uncomment the following line if necessary. # uid = …
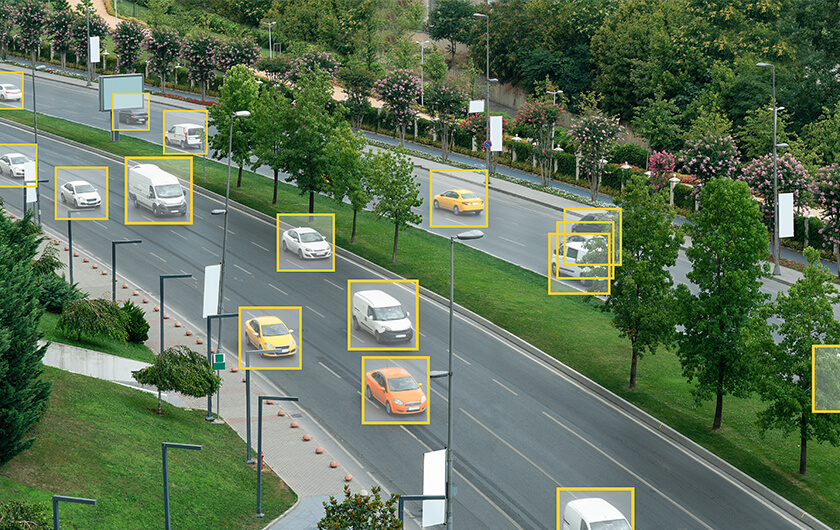
More Freedom on the Highway: Artificial Intelligence Lifts Malaysia’s Toll Barriers
Chee How Lim worked as an aerospace engineer in Malaysia. He wanted to start a business that would really take off. Today, his company, Tapway, is riding a wave of people using computer vision and AI in Southeast Asia. The Kuala Lumpur company’s biggest project to date was made possible by a request for help …
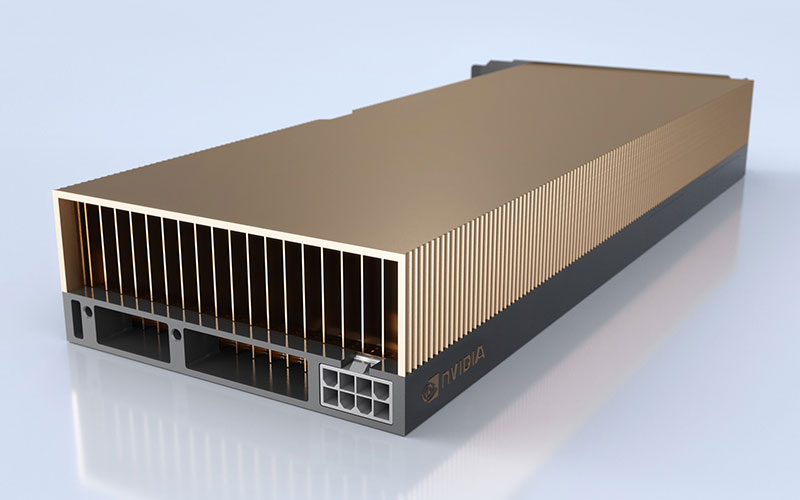
NVIDIA A30 GPU
NVIDIA A30 Tensor Core GPUs provide increased performance for every enterprise workload. It enables secure speedups across different workloads, including AI inference at scale and high-performance computing (HPC) applications, thanks to NVIDIA Ampere architecture Tensor Cores and Multi-Instance GPU (MIG). A30 allows an elastic data center and delivers maximum value for organizations by combining rapid …
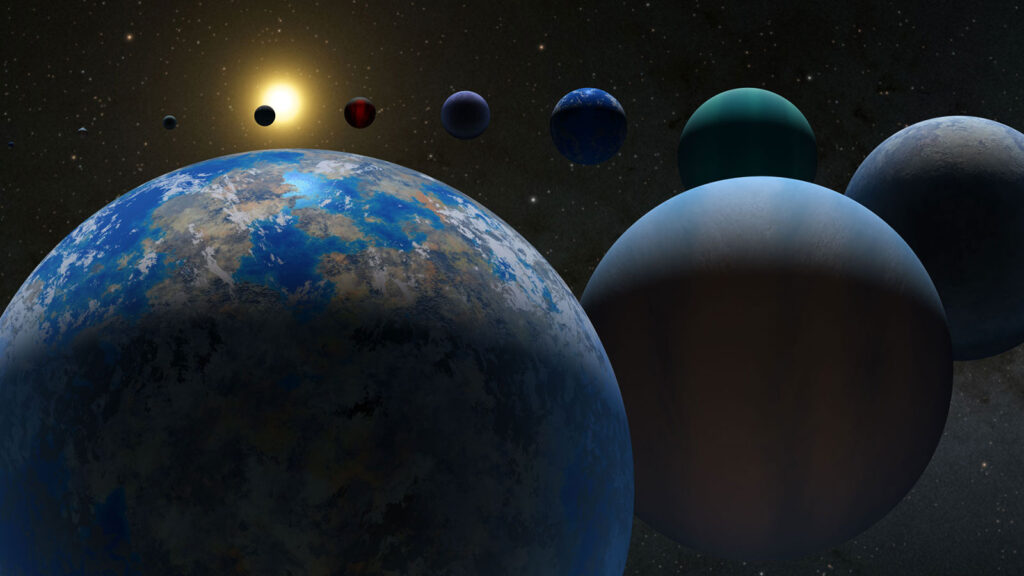
Exoplanets’ Skies: Astronomers Describe the Planets’ Climates
The atmospheres of distant planets have been described in unprecedented depth in a report published today. Scientists investigated 25 exoplanets (planets that orbit stars outside our solar system) in an effort to learn more about the universe. To be more specific, scientists looked at exoplanets with temperatures over 3,000 degrees Fahrenheit, common on hot Jupiters, …

What is a Dedicated Server?
When you originally created your website, you probably chose shared hosting, like many other new site owners. It is, after all, the cheapest alternative, and budget is crucial. It’s crucial to know when to upgrade to something more robust as your website grows. There are numerous possibilities available, and you may be wondering, “What is …
Why Do You Need Dedicated Hosting?
Tired of other sites on the same server slowing down your website? Do you require additional capacity to accommodate your increasing number of website users and customers? Is your existing web hosting plan no longer meeting your needs? If this is the case, it may be time to upgrade to dedicated hosting. What is Dedicated …
What Is NetOps?
NetOps is a network operations approach that emphasizes agility and rapid deployments. Techniques like automation, virtualization, and orchestration are used in this strategy. Why is a NetOps strategy required? To stay up with customer expectations, today’s digital organization must be more flexible than ever. Continuous network automation and validation are intended to simplify network operations …
route and netstat commands are slow in listing the routing table
Instead, use the ip route, route -n, or netstat -rn commands. Contact the DNS server administrator to find out why queries are taking so long. The DNS server takes almost 10 seconds to return a reverse name lookup on the gateway, as seen in the output of dig. Query time: 8880 msec Time the commands …
How to increase number of routes per router exceeding default 30 routes in Openstack Platform 15
The max_routes parameter in neutron.conf can be increased to accommodate more routes per router. # crudini --set /var/lib/config-data/puppet-generated/neutron/etc/neutron/neutron.conf DEFAULT max_routes 45 Restart the neutron_api service. # podman restart neutron_api This parameter must be set in neutron.conf after the service has been restarted, and then more than 30 routes can be added to a router. # …
What are Containers?
This guide examines the role of containers in cloud computing, highlights key benefits, and takes a look at the growing ecosystem of related technologies, including Docker, Kubernetes, Istio, and Knative. Containers are executable software units in which application code, as well as its libraries and dependencies, are packaged in standard ways so that they can …

Artificial Intelligence AI and Machine Learning ML in Cybersecurity
Artificial intelligence (AI) and machine learning (ML) are present in every second of our lives, whether we realize it. Smart devices decide when to turn on our heaters and lights the moment we wake up, social media uses complex algorithms to determine what news to promote to us, and Google Maps guides us through our …

What is Scareware?
Scareware is a term frequently used to refer to a cyberattack tactic that scares people into visiting bogus or infected websites or downloading malicious software (malware). Scareware may manifest itself in pop-up advertisements that appear on a user’s computer or via spam email attacks. Scareware attacks are frequently launched via pop-up messages that appear on …
How do I set the default IPv6 policy routing route in NetworkManager?
I have a route configuration file that contains the default route for a routing table similar to this, but it does not apply during boot. route6-bond0 default via 2001::ff table 1 # ip -6 route show table 1 Error: ipv6: FIB table does not exist. Dump terminated Using the following syntax, add the route to …