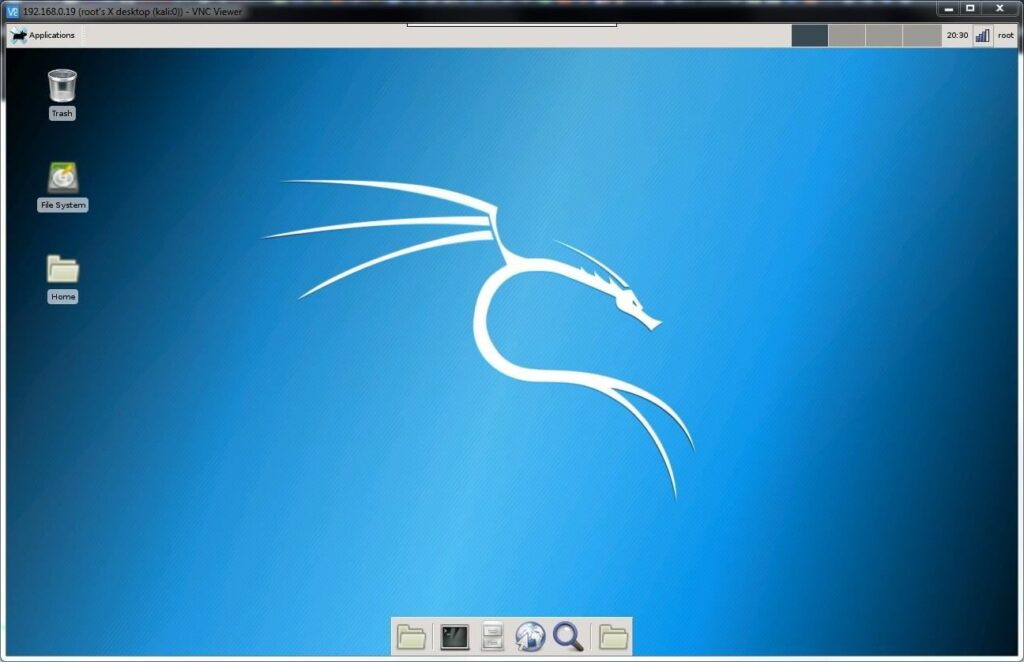
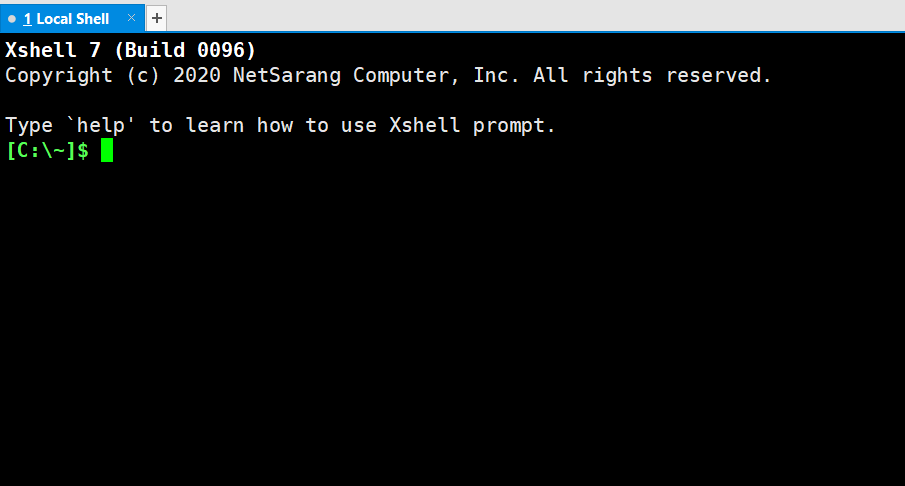
This is a quick guide to installing VNC on Debian 9 and Kali Linux Login to your server as root. Install VNC server with apt-get install tightvncserver If you get the following error then you can install tightvncserver from Debian or Kali installation ISO image. root@server:/home/user# apt install tightvncserver -y Reading package lists... Done Building …