Spear-phishing emails are responsible for over 90% of cyber attacks and data breaches. Spear phishing emails are similarly responsible for 95% of all attacks on enterprise networks. So, what is it about phishing emails in general, and spear-phishing emails in particular, that makes them so dangerous? And how can individuals and businesses guard against such an intrusive tactic?
Overview
Spear phishing is a type of phishing attack that is much more targeted. The perpetrator does not simply send a generic email to thousands or tens of thousands of people in this case. Instead, they send each of their targets a personalized email. That email is only sent after the perpetrator has done their homework and has specific information about their victim that will motivate them to act. Those key details allow the perpetrator to craft the email in such a way that it instills trust in their victim and encourages them to do something they might not have done otherwise.
Human greed or fear are usually the targets of spear-phishing attacks. This means they’ll either bribe targets with money, discounts, or bargains, or they’ll threaten them into acting by threatening to freeze their checking, PayPal, or eBay accounts.
To persuade their victim to act, the perpetrator of a spear-phishing attack will first locate them and gather critical information in order to ensure that whatever tactic they use is credible. For example, they might look up a person’s profile on a social networking site and extract information such as their target’s email address, geographic location, workplace, friends list, and any recent large purchases and where they came from. Such details may appear innocuous on their own, but when combined, they enable the perpetrator to craft a dangerously effective email.
The perpetrator will use the information to send a highly convincing but ultimately fraudulent message as a friend, colleague, boss, or other familiar entity in their spear-phishing email. To make emails appear more convincing, hackers use a combination of email spoofing and dynamic URLs.
How does Spearphishing Work?
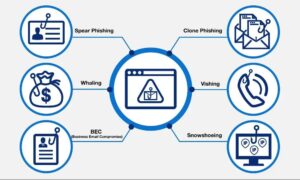
Any cyber or phone-based scheme designed to trick a victim into giving up personal information is referred to as phishing.
This information is then used in some kind of scam. It’s a common hack, and the majority of phishing schemes target thousands of people in the hopes of fooling a few. Consider the well-known “Nigerian Prince” con. Thousands of people are targeted in this phishing scam, which sends emails offering a large sum of money in exchange for the recipient transferring money on their behalf. The majority of people will delete the email, but there will always be those who do not. Those who fall prey to the scam could lose thousands, if not tens of thousands of dollars.
Phishers have become more specialized as more people have become aware of such scams and as business, IT groups, and email servers have tightened up security. This is where spear phishing, a hacking technique, was born.
Examples
The following are some examples and scenarios of how spear phishing works and appears:
Spear Phishing an Individual
The perpetrator learns which bank their victim uses and, using a spoofed email and stolen website credentials, sends the victim an email claiming the account has been hacked. Fear-mongering will be used in that email to persuade the target to call a number or click a link to provide confidential banking information (such as username and password) to prove they are the legitimate account holder. The assailant will then use this information to steal money.
Spear Phishing a Business
A spear-phishing attack on a business is similar to one on an individual in that the perpetrator will conduct research before drafting a legitimate-looking scam. The scale, however, is different. When cyberthieves uncovered key details about Ubiquiti Networks Inc. executives, the networking company learned the hard way. The thieves then used those details to create spoof communications that appeared to be from the firm’s executives, instructing the finance department to make $46.7 million in unauthorized international wire transfers.
How to Avoid Spearphishing
Spear phishing attacks may appear to be legitimate, but they are extremely dangerous. Individuals and businesses can use the following tips to help prevent perpetrators of such attacks from harvesting key data and using it to gain access to critical accounts:
- Don’t give out personal information online, such as your phone number. Every person should avoid sharing their phone number on social media platforms and entering their phone number into unknown (or even well-known) websites and mobile applications. Phone numbers are just as important as social security numbers in identifying a person and their complete financial history. A person can essentially take over all of a person’s financial accounts using techniques like SIM swapping and phishing scams.
- Never open an unknown email attachment or link, especially if it comes from a financial or business institution. Use best practices for email security. Spear phishing attacks frequently send emails impersonating a trusted institution that the victim is familiar with, such as Bank of America, Amazon, or eBay. Any emails received via personal business email should not be taken at face value. To investigate claims and conduct business as usual, never click a link from such an organization; instead, open a new browser window and go directly to the institution’s website. Any other emails you receive, whether from friends, favorite bloggers, or nonprofit organizations, should be carefully considered. Always check the anchor text before entering personal information or other sensitive information into a link clicked from an email.
- Use caution when sharing too much information on social media. Keep an eye on their social media profiles for personal information and who has access to it. Keep your privacy settings high and don’t accept friend requests from people you don’t know.
- Every company should implement a comprehensive data security program. Data protection programs consist of a combination of user education and security awareness training on best digital security practices, as well as the implementation of a comprehensive cyber security solution to prevent data loss from cyber attacks such as spear phishing.
- Don’t send emails containing sensitive information. Emailing employees from a reputable-looking address and requesting sensitive information such as passwords or business banking information is a common spear phishing tactic.
No one is immune from becoming a target of cybercriminals. If you have information on the internet or have downloaded applications to your smartphone, you could be a target for this and other sophisticated cyber attacks. The best way to avoid becoming a victim is to remain vigilant at all times. To ensure that business assets are similarly protected, keep the information confidential, never trust outside sources, and contact an experienced and professional security solutions team.