Introduction
Confidential computing is a security paradigm that protects sensitive data while being processed. In traditional computing, data is processed in the clear, meaning that it is visible to all components of the computing system, including the operating system, applications, and network.
It makes it vulnerable to attacks such as eavesdropping, malware, and unauthorized access. Confidential computing, on the other hand, creates a protected area where data can be processed without being exposed to other parts of the system.
It can help to minimize the risk of data breaches and other security incidents. Confidential computing is becoming more critical as organizations use the cloud and third-party providers to manage their IT infrastructure.
Data is often shared among multiple users and applications in these environments, increasing the risk of security breaches. Confidential computing can ensure that data remains confidential, even in shared environments.
How does confidential computing work?
Enclaves and trusted execution environments are essential concepts in confidential computing: enclaves protect data from the rest of the system by providing remote memory regions. In contrast, trusted execution environments offer a secure environment for running applications.
Either hardware-based or software-based approaches can achieve confidential computing. Hardware-based techniques use specialized processors like Intel SGX to create secure enclaves. Therefore, we can process the data without exposing it to the rest of the system.
Software-based approaches use virtualization and containerization technologies to create isolated environments for data processing.
For availing GPU servers with professional-grade NVIDIA Ampere A100 | RTX A6000 | GFORCE RTX 3090 | GEFORCE RTX 1080Ti cards. Linux and Windows VPS are also available at Seimaxim.
Hardware-Based approaches
Hardware-based approaches to confidential computing rely on specialized processors that provide secure enclaves for data processing.
These processors are designed to provide a safe execution environment isolated from the rest of the system. One example of a hardware-based approach is Intel SGX.
Intel SGX
Intel SGX (Software Guard Extensions) creates secure enclaves where data can be processed without exposure to the rest of the system, making it a hardware-based approach to confidential computing.
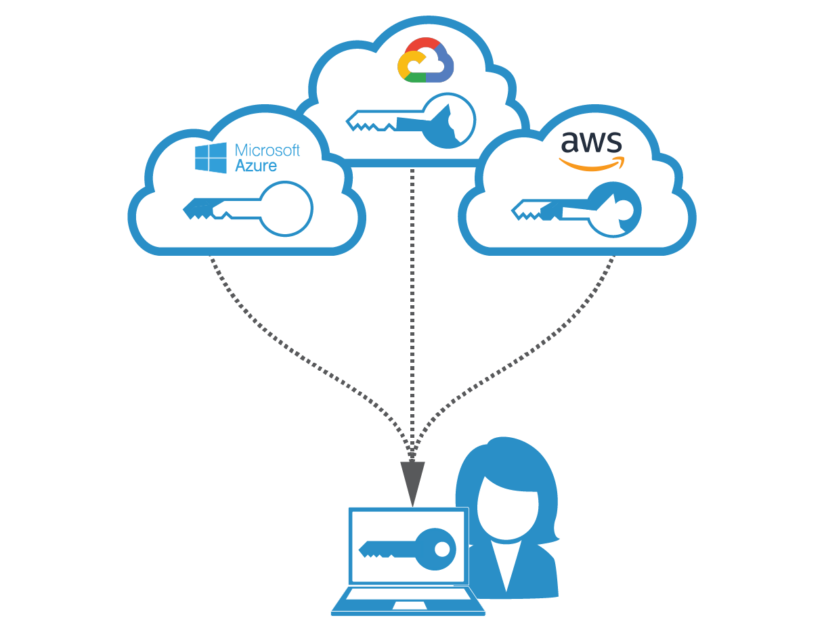
Some cloud service providers, such as Microsoft Azure and Google Cloud Platform, support SGX, available on specific Intel processors. SGX creates a secure enclave, an isolated region of memory protected from the rest of the system.
It covers data from other system components, including the operating system and other applications. The enclave is encrypted and can only be accessed by the application that created it.
Software-Based approaches
Software-based approaches to confidential computing rely on virtualization and containerization technologies to create isolated environments for data processing.
These environments are designed to be secure and isolated from the rest of the system. One example of a software-based approach is containerization.
Containers are lightweight and portable and can package applications and their dependencies. Designers create isolated enclaves from the host system to improve security.
Containerization is a technology that enables the creation of isolated environments for applications. Containerization can be used to create remote environments for data processing.
It can help to reduce the risk of data breaches and other security incidents. By running applications in containers, data can be processed in a secure and isolated environment.
Trusted execution environments
Trusted execution environments are another important concept in confidential computing. It also provides a secure environment for running applications and can be used to protect sensitive data.
It is often used in mobile devices and other embedded systems.
Benefits of confidential computing

Confidential computing offers several benefits to organizations that need to protect sensitive data. Organizations can lessen the risk of data breaches and other security incidents by keeping data confidential.
Here are some of the critical advantages of confidential computing
Enhanced security
Confidential computing provides a secure execution environment for processing sensitive data. By isolating data and applications from other components of the computing system, personal computing can help to reduce the risk of attacks such as eavesdropping, malware, and unauthorized access.
Confidential computing allows sensitive data to be processed in a protected environment without the risk of data leakage, unauthorized access, or other cyber attacks. It can help organizations to protect sensitive data and maintain customer trust.
Compliance
Many organizations are subject to regulatory requirements, such as GDPR and HIPAA, which require the protection of sensitive data. Confidential computing can help organizations to comply with these requirements by providing a secure environment for data processing.
With confidential computing technologies, organizations can ensure they meet the highest data privacy and security standards.
Data privacy
Confidential computing can help organizations protect their customers’ privacy by ensuring that sensitive data is not exposed to unauthorized users.
It can help organizations to build trust with their customers and enhance their reputation.
By encrypting sensitive data and keeping it isolated from other components of the computing system, confidential computing can help to prevent unauthorized access and data breaches.
Flexibility
Hardware- and software-based approaches for implementing confidential computing allow organizations to select the appropriate solution that caters to their requirements.
Hardware-based strategies may be more expensive but offer higher security, while software-based strategies may be more affordable and easier to implement. This flexibility allows organizations to choose the best approach to their needs and budgets.
Cloud computing
Confidential computing is becoming increasingly important as organizations use cloud computing and third-party providers to manage their IT infrastructure.
Confidential computing can ensure that data remains confidential, even in shared environments. Organizations can confidently move their sensitive data and applications to the cloud with personal computing, as they will be protected against data breaches and cyber-attacks.
Cost-Effective
Confidential computing can help organizations save money on infrastructure costs. It can help organizations to facilitate their IT costs and invest more in their core business activities.
By using confidential computing, organizations can use commodity hardware to secure sensitive data and reduce reliance on expensive security appliances.
Competitive advantage
Confidential computing can help organizations gain a competitive advantage by offering customers superior data security and privacy.
It can help differentiate organizations from competitors and attract new customers concerned about data security and privacy.
Challenges and limitations of confidential computing
The technology can protect corporate and government databases, personal medical records, and biometric data.
Additionally, it allows developers to create cloud-based applications with end-to-end encryption, eliminating the risk of data breaches or hacks.
However, while the benefits of confidential computing are substantial, several challenges still need to be addressed.
Implementing and maintaining confidential computing systems entail high costs.
Furthermore, it requires increased technical expertise and a deep understanding of the underlying infrastructure and software architecture.
In addition, businesses need to have specialized hardware and secure networking configurations to use confidential computing in the cloud.
Furthermore, some organizations have to rely on trusted execution environments, which the cloud service provider provides, but not all cloud providers support confidential computing.
As a result, this limits the scalability of confidential computing and increases the potential risk of malicious activity. Finally, there are questions about the efficacy of confidential computing for long-term data protection.
In particular, its security capabilities might not be sufficient for mission-critical or sensitive data.
As a result, organizations need to take a comprehensive risk-based approach to evaluate the security of confidential computing systems before deployment.
While confidential computing offers several advantages over traditional security measures, its limitations remain.
For organizations to fully leverage the benefits of this technology, they need to carefully assess their risk profile and choose the appropriate solution for their particular environment.
Applications of confidential computing
Improved data protection and security
Confidential computing protects data at the application layer, even when the underlying system is untrusted.
By placing the data within a trusted execution environment (TEE) such as an SGX enclave, users can have peace of mind knowing that the data is safe and secure from unauthorized access or modification.
Faster and easier deployment of data processing
Confidential computing helps organizations quickly deploy applications on different hardware systems, cloud platforms, and on-premises servers without costly hardware.
This allows organizations to leverage their existing resources, eliminating the need to spend additional time and money on hardware modifications or other training for their staff.
Increased privacy and compliance
Confidential computing makes it easier to adhere to strict privacy and compliance standards.
Organizations can ensure the encryption and protection of all data throughout its entire lifecycle by deploying confidential computing applications. It reduces the risk of a privacy or compliance breach.
Streamlined development and testing
Developers can quickly and easily create confidential computing applications for the production environment.
This eliminates the need to invest time and money in setting up test environments and verifying data protection requirements.
Enhanced scalability and flexibility
With confidential computing applications, organizations can quickly scale up or down their applications according to the ever-changing business needs.
Using TEEs, developers can provide customers with fast, efficient, and secure data processing without making any significant infrastructure changes.
Faster analysis of big data set
By taking advantage of secure, private computation models such as Secure Multi-Party Computing (MPC), developers can efficiently process big data sets without exposing individual data points to a third party.
Secure interactions between devices
Confidential computing applications encrypt data even while interacting with other devices, such as connected cars, phones, or sensors.
This makes it impossible for malicious actors to intercept the data in transit and prevents them from stealing sensitive information.
Case studies of confidential computing
Confidential computing is a form of computing that has recently gained attraction in both public and private domains. Therefore, companies increasingly leverage confidential computing solutions to protect sensitive data while in use.
In the healthcare sector, where patient information must remain private but accessible to healthcare practitioners and patients, this holds particularly true.
Confidential computing aims to ensure the secure storage and use of sensitive data using techniques such as fast multi-party computation and encryption.
Secure multi-party computation (MPC) involves multiple parties participating in a single computing operation, with access limited to the output and an inability to view the information.
Meanwhile, encryption also helps protect the confidentiality of the data by making it virtually impossible for third parties to view or decipher.
Companies using confidential computing
One company utilizing confidential computing is Xealth, a Seattle-based digital health platform. The company uses secure cloud environments for medical record sharing and medical management for providers.
By using MPC and encryption, Xealth can secure the data so that patients are only sharing with their healthcare providers the necessary data and protecting any sensitive information they don’t want to see by any third party.
Another company taking advantage of confidential computing is Iress, an Australian-based financial services company.
To protect customer data while it is in use, Iress leverages both MPC and encryption by breaking up sensitive data into different encrypted chunks and utilizing MPC to operate on each one separately. Iress ensures customer data remains confidential throughout its usage and the associated transactions.
Lastly, Ford Motors also uses confidential computing for the FordPass Connected Car service. The company uses cryptography, authentication, encryption, and cloud services to secure sensitive data.
The company can continue to develop its Connected Car technology without putting customers at risk by using this advanced technology.
Confidential computing can use secure, real-time access to sensitive data without sacrificing the privacy of its owners, as demonstrated by these case studies.
In each of these scenarios, companies could successfully secure customer data without any third party being able to view the data.
The customers can rest assured that their data is protected.
As such, confidential computing will likely become a core component of secure computing in the years to come.
Confidential computing innovations
Confidential computing is a rapidly evolving field with much potential for innovation and growth. As more and more data is generated and processed, ensuring its confidentiality is becoming increasingly important.
Trust issues
One of the main challenges facing confidential computing is the issue of trust. The effective functioning of confidential computing requires a high level of trust among the different parties involved.
This includes the data owners, the service providers, and the end-users. Ensuring secure and confidential handling of data becomes difficult without trust.
Researchers are exploring new approaches to building trust in confidential computing systems to address this challenge. One promising approach is to use blockchain technology to create a decentralized trust network.
By leveraging blockchain’s security and transparency, creating a system that provides secure and confidential data handling may be possible, which can instill confidence in all parties involved.
Advanced encryption techniques
Another significant trend in confidential computing is the use of advanced encryption techniques. Researchers are exploring new methods of encrypting data to enable cloud-based services to process it without exposing it to the service provider.
Third-party services could process data confidentially through an approach known as “homomorphic encryption,” ensuring that the data remains confidential.
Risk of interoperate
Finally, there is a growing need for standards and best practices in confidential computing. As more organizations adopt these technologies, there is a risk that different systems cannot interoperate effectively.
To address this challenge, industry groups are working to develop standards and best practices for confidential computing. These efforts will be critical to ensuring that confidential computing can achieve its full potential in the years ahead.
In terms of plagiarism, confidential computing has the potential to provide a more secure way of sharing and processing data without the risk of intellectual property theft.
Encryption and other security measures can protect sensitive data from unauthorized access and manipulation.
Confidential computing vs. Traditional security approaches
Confidential computing and traditional security approaches represent different approaches to protecting sensitive data and ensuring the security of computing systems.
While traditional security approaches rely on perimeter-based security and access control measures, confidential computing emphasizes the need for data encryption and protection within the system itself.
Here’s a more detailed description of the differences between confidential computing and traditional security.
Traditional security approaches
Establishing a perimeter of security around the network or application is the basis of traditional security approaches for protecting computing systems.
These approaches typically rely on firewalls, intrusion detection and prevention systems, access controls, and other security measures to prevent unauthorized access and data breaches.
Traditional security approaches work by creating a secure perimeter around the computing environment. It includes all the components that make up the system.
Only authorized users or entities can have access to the system. So, any attempts to breach the perimeter are detected and blocked. However, traditional security approaches have several limitations.
First, they are vulnerable to advanced threats such as zero-day attacks and targeted attacks, which can bypass perimeter-based security measures.
Secondly, the storage or processing of sensitive data within the system itself may render traditional security approaches ineffective in its protection. This is where confidential computing comes in.
Confidential computing
is a security paradigm emphasizing the need for data encryption and protection within the system.
It enables organizations to protect sensitive data by creating secure enclaves. Therefore, It processes the data without exposing it to other components of the computing system.
Hardware- and software-based enclaves can protect data at rest and in transit.
Using confidential computing techniques, like encrypting and decrypting, we can ensure that data will remain safe from exposure to the outside environment within the secure enclave.
This means that even if an attacker gains access to the system, they cannot access the encrypted data without the encryption key.
Confidential computing also enables organizations to process data in the cloud or other shared environments securely. It also ensures that data remains confidential and protected.
Compared to traditional security approaches, confidential computing provides several advantages.
First, confidential computing can protect data from internal and external threats, including insider attacks and data breaches.
Second, confidential computing can help organizations to comply with regulatory requirements, such as GDPR and HIPAA. It ensures that sensitive data is safe at all times.
Third, confidential computing can enable secure collaboration and data sharing among different parties without compromising data privacy and security.
Conclusion
Confidential computing is another security approach and a paradigm shift in how we approach data security in the digital age. As online data sharing increases and our world becomes more interconnected, we can observe the need for enhanced security measures.
It is becoming clear that traditional security approaches are no longer sufficient.
What is genuinely mind-blowing about confidential computing is potential. It holds for transforming the way we think about data security.
With confidential computing, we can envision a world where data privacy is not just a matter of compliance or risk management but a fundamental human right.
Confidential computing can unlock new opportunities for innovation, research, and discovery by enabling secure collaboration and data sharing among different parties. It also safeguards sensitive data from unauthorized access and misuse.
The future of confidential computing is bright, but it also presents new challenges and opportunities.
As more organizations adopt confidential computing, we must develop new standards, best practices, and governance frameworks to ensure data protection and ethical use.
To ensure the adoption of confidential computing at scale across different industries and regions. We must also address data sovereignty, ownership, and interoperability issues.
In conclusion, confidential computing represents a bold new vision for data security. It can transform how we use and share sensitive data in the digital age.
As we navigate the challenges and opportunities of this new paradigm, we must remain vigilant, innovative, and collaborative to ensure that confidential computing can deliver on its promise of a more secure, private, and connected world.